That is exactly what Browser Relay is for. The current Chrome Web Store listings describe it as a Chrome extension that attaches OpenClaw to your existing Chrome tab through a local CDP relay server, letting the agent drive and observe the tab programmatically. The official OpenClaw browser docs frame the choice more broadly as using either the default isolated OpenClaw-managed browser or the user profile path when your existing logged-in browser session matters.
This guide explains what OpenClaw Browser Relay actually does, how it compares with the managed browser, when it is the better option, what usually goes wrong during setup, and how to use it more safely.
What OpenClaw Browser Relay is
OpenClaw Browser Relay is the bridge between your normal Chrome tab and your OpenClaw agent. Instead of opening a separate isolated browser profile, it lets OpenClaw attach to a tab you already have open and control it through Chrome DevTools Protocol, usually shortened to CDP. The Chrome Web Store listing describes it as attaching OpenClaw to an existing Chrome tab via a local CDP relay server, while the official docs describe the user profile path as the way to use your real signed-in Chrome session when that matters.
In plain language, Browser Relay is for situations where you want OpenClaw to work inside your real browsing session rather than inside the separate OpenClaw-managed browser.
That matters when:
- you are already logged into a site
- you need your saved cookies or sessions
- you want the agent to act in the exact tab you are viewing
- you want browser automation without switching to a separate window
How Browser Relay differs from the managed browser
This is the main choice most people are really making.
The official OpenClaw browser docs say the default setup is the isolated OpenClaw browser, and they recommend using profile="user" only when existing logged-in sessions matter and the user is at the computer to click or approve any attach prompt. They also note that the managed OpenClaw browser does not require the extension.
So the difference looks like this:
Managed browser
- • isolated from your normal browsing
- • no extension required
- • safer default for general automation
- • better when you do not need existing login state
Browser Relay
- • attaches to your real Chrome tab
- • uses your existing signed-in session
- • better for workflows that depend on live user context
- • usually requires you to be present to attach and approve access
That split shows up clearly across both the official docs and the ranking pages around this keyword.
When Browser Relay is the better choice
Browser Relay is the better option when the tab itself matters.
Use it when:
- you need OpenClaw to work inside your normal Chrome session
- the site requires your existing login state
- you want the AI to operate on the page you are already looking at
- your workflow depends on real user context, not a fresh isolated browser
The official docs explicitly say to prefer the user profile path when existing logged-in sessions matter. That is the clearest signal of intent behind Browser Relay.
Typical use cases include:
- logged-in web apps
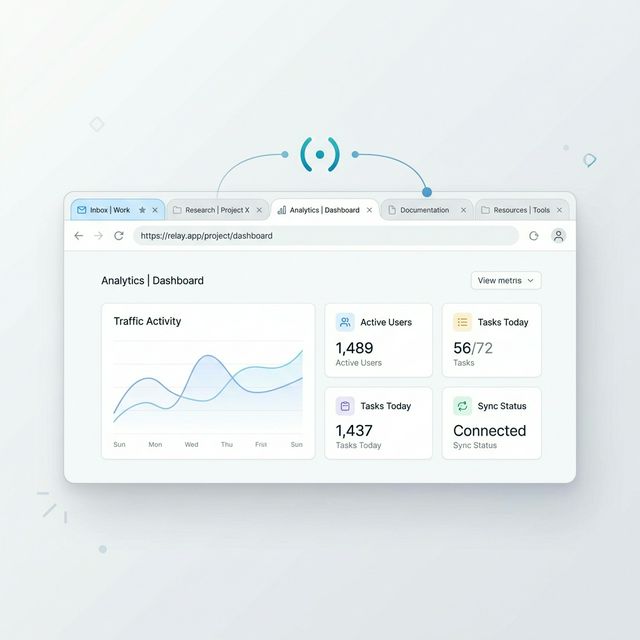
- inbox or dashboard workflows
- admin panels where your session is already active
- sites with MFA or approval flows you will handle live
- research and browsing tasks where page context matters
When the managed browser is usually better
A lot of ranking pages around Browser Relay make the extension sound like the default best option. The official docs do not.
The official browser docs say the default is the isolated OpenClaw browser and recommend the user profile path only when needed. That means the managed browser is usually the better starting point when:
- you do not need existing logins
- you want cleaner isolation
- you want fewer extension steps
- you want a simpler browser automation path
The Linux troubleshooting docs reinforce this by suggesting the managed browser as a fix path when extension relay is not attached or not working.
So Browser Relay is not the universal answer. It is the answer for specific cases where real-session access matters.
How OpenClaw Browser Relay works
At a high level, Browser Relay works like this:
- You install the Chrome extension
- You open a Chrome tab
- You attach the relay to that tab
- OpenClaw connects through the local CDP relay
- The agent can then observe and control the tab
The Chrome Web Store description says the extension connects your browser to the OpenClaw automation gateway running on your machine, and that with one click on a Chrome tab you attach a local CDP relay that lets OpenClaw drive and observe the tab programmatically.
The official docs also describe the browser CLI as the place to manage the browser control server and run browser actions such as tabs, snapshots, screenshots, navigation, clicks, and typing.
So Browser Relay is not just passive visibility. It is the control path that lets the agent interact with the live tab.
Why Browser Relay can feel more powerful
Browser Relay often feels more powerful because it gives the agent access to your real browser context.
That means it can potentially work with:
- your current signed-in site
- your current tab state
- pages that are already open
- actions that are easier in a live session than in a fresh isolated browser
That is why several ranking pages emphasize things like reading page content, clicking links, filling forms, navigating live sites, and working through real browser sessions rather than a separate automation profile.
For the right workflow, that is a real advantage.
Why Browser Relay can also be riskier
The same thing that makes Browser Relay useful also makes it riskier.
When OpenClaw controls your real browser tab, it is potentially working with your actual signed-in sessions, saved state, and live context. The official docs recommend this route only when existing logged-in sessions matter and the user is at the computer, which is a strong sign that this mode should be treated more carefully than the isolated browser.
The practical risks are:
- acting inside a sensitive logged-in account
- triggering actions in a real user session
- relying on a host-local connection path that can break or misbehave
- exposing more of your live browsing state than you intended
That does not mean Browser Relay is unsafe by default. It means you should use it because you need it, not just because it sounds more powerful.
What the current ranking pages are getting right
After checking the pages already ranking for this topic, a few patterns repeat.
Most ranking pages correctly focus on:
- connecting OpenClaw to your existing Chrome tabs
- using CDP or a relay server
- letting the agent click, read, navigate, and interact with the page
- the advantage of working with your real browser instead of a separate one
Those are the right core ideas.
What many ranking pages leave out
A lot of the ranking pages and extension listings lean hard into the convenience story, but they often underplay the tradeoffs.
The official docs add important nuance that many third-party pages gloss over:
- the isolated OpenClaw browser is still the default
- the user profile path is for cases where logged-in sessions matter
- WSL2 plus Windows Chrome has special limitations
- the relay expects a live attached tab
- host-local assumptions matter for certain browser modes
That nuance matters because it changes the decision from "Should I install the extension?" to "Do I actually need this mode for my workflow?"
Biggest setup and compatibility issues
Browser Relay is useful, but it is also where a lot of people run into friction.
1. No attached live tab
The Linux troubleshooting docs say that the user profile path expects the OpenClaw browser extension to be attached to a live tab. Their fixes include using the managed browser or installing the extension and clicking the extension icon to attach it.
That means one common failure is simple: the extension exists, but the tab is not actually attached.
2. WSL2 plus Windows Chrome confusion
The official troubleshooting docs for WSL2 and Windows say to use the existing-session or user path only when the Gateway runs on the same host as Chrome. For WSL2 Gateway plus Windows Chrome, the docs say to prefer raw remote CDP because Chrome MCP is host-local and not a WSL2-to-Windows bridge.
This is one of the most important compatibility notes in the current docs, and it is the kind of thing many ranking pages skip.
3. Wrong browser mode for the job
Sometimes users install Browser Relay when they really should be using the managed OpenClaw browser. The official docs make clear that managed mode is still the default.
4. Assuming every extension listing is official
Search results for this topic now include multiple Chrome Web Store listings and unofficial variants. Some explicitly say they are unofficial or tailored to specific environments.
That makes it important to verify which extension you are using and whether it matches your setup.
Best quick workflow: install, test, choose, then expand
If you want the least painful Browser Relay setup, this is the simplest path.
Install. Start with the extension and official browser docs, not random setup threads. Confirm whether your real need is user-session access or just browser automation.
Test. Attach one live Chrome tab and confirm the relay works before trying to automate everything. The troubleshooting docs make it clear that the attached live tab requirement matters.
Choose. If your workflow does not actually depend on existing signed-in sessions, switch back to the managed browser. The official docs make that the default for a reason.
Expand. Only after the connection works cleanly should you move into more complex logged-in workflows, browser actions, or sensitive tabs.
How QuestStudio helps
QuestStudio is not a browser relay itself, so it is not a direct replacement for Browser Relay. Where it helps is around the planning and workflow side.
If you are designing OpenClaw browser workflows, QuestStudio can help you:
- map when to use the managed browser vs relay mode in Planning Lab
- document browser tasks and safe-use rules
- organize prompt patterns in Prompt Lab
- plan browser-based automations before you connect them to a live session
That is useful because Browser Relay is most valuable when the workflow is already clear. The real decision is usually not "Can OpenClaw control the browser?" It is "Which browser mode should I trust for this task?"
Related guides
FAQ
What is OpenClaw Browser Relay?
When should I use Browser Relay instead of the managed browser?
Does Browser Relay control my real Chrome tab?
Why is Browser Relay not working?
Is Browser Relay safer than the managed browser?
Do I need the extension for all OpenClaw browser automation?
Conclusion
OpenClaw Browser Relay is useful because it lets the agent work inside the browser session you already use. That can make logged-in workflows, live tabs, and real-context automation much easier. But it is not the universal default, and the official docs are clear about that. The managed browser is still the default isolated path, while Browser Relay is the better choice when your real session matters enough to justify it.
So the smartest way to use Browser Relay is not to install it everywhere first. It is to use it only when your workflow genuinely depends on your existing Chrome context.